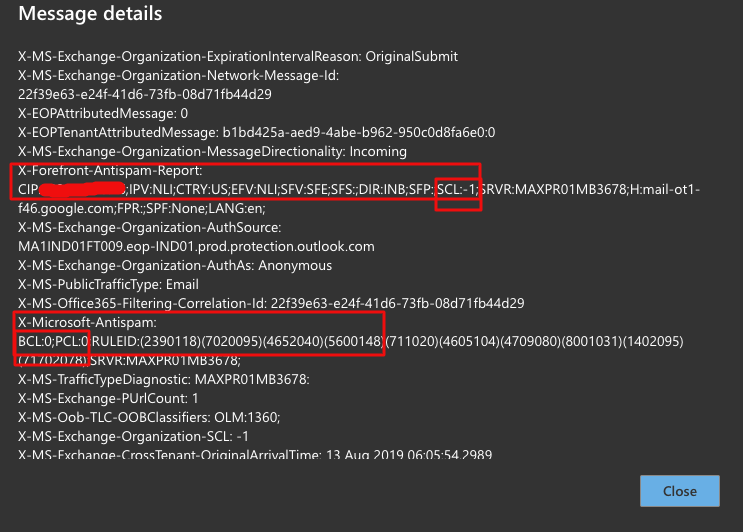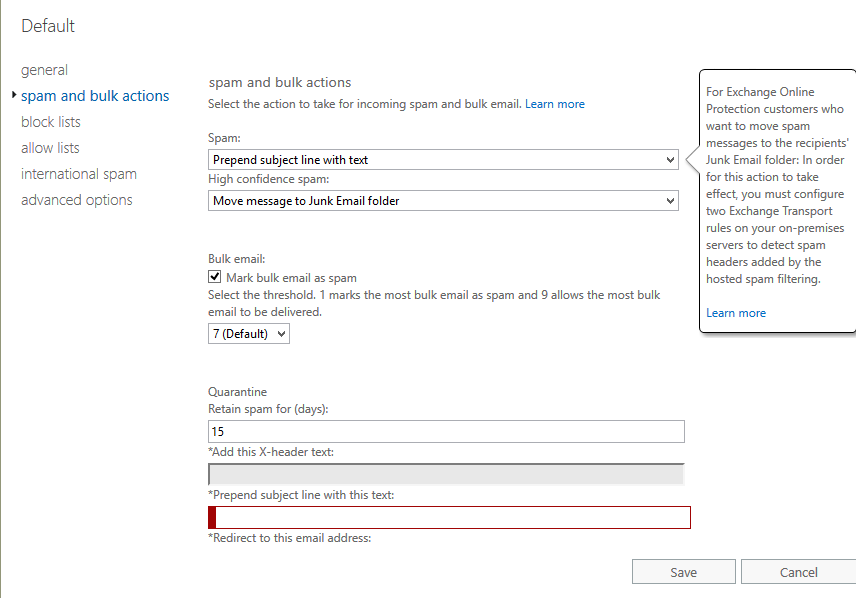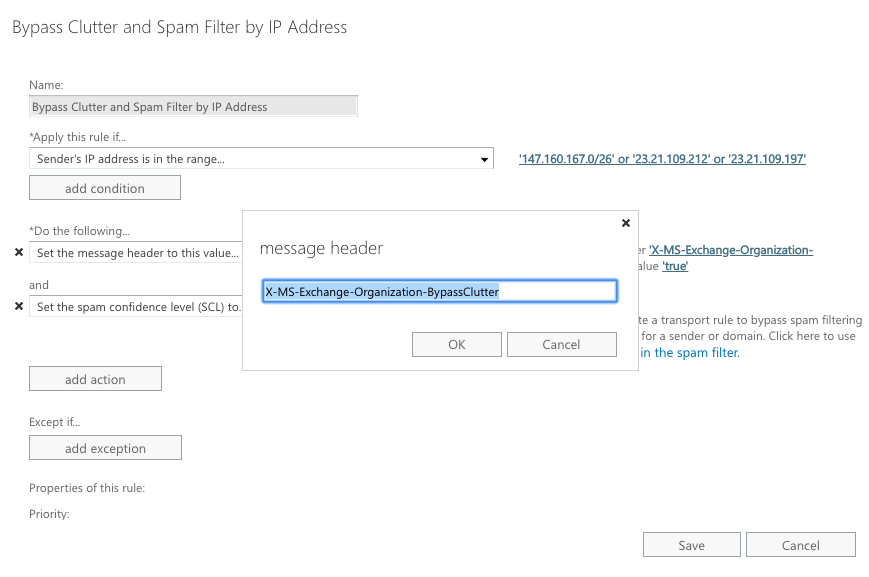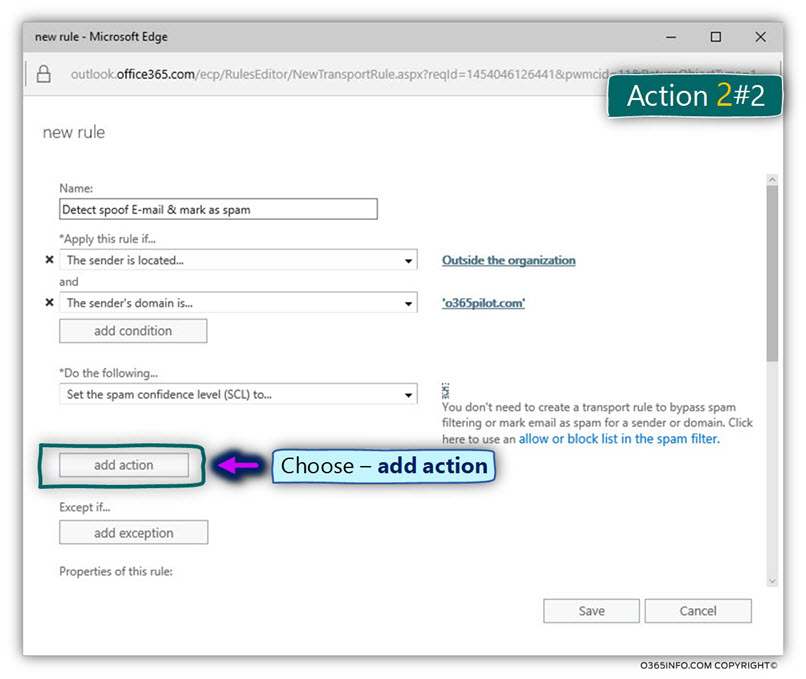
Detect spoof E-mail, mark spam , SCL | Detect spoof E-mail and mark the E-mail as spam using Exchange Online rule |Part 4#12 | o365info.com
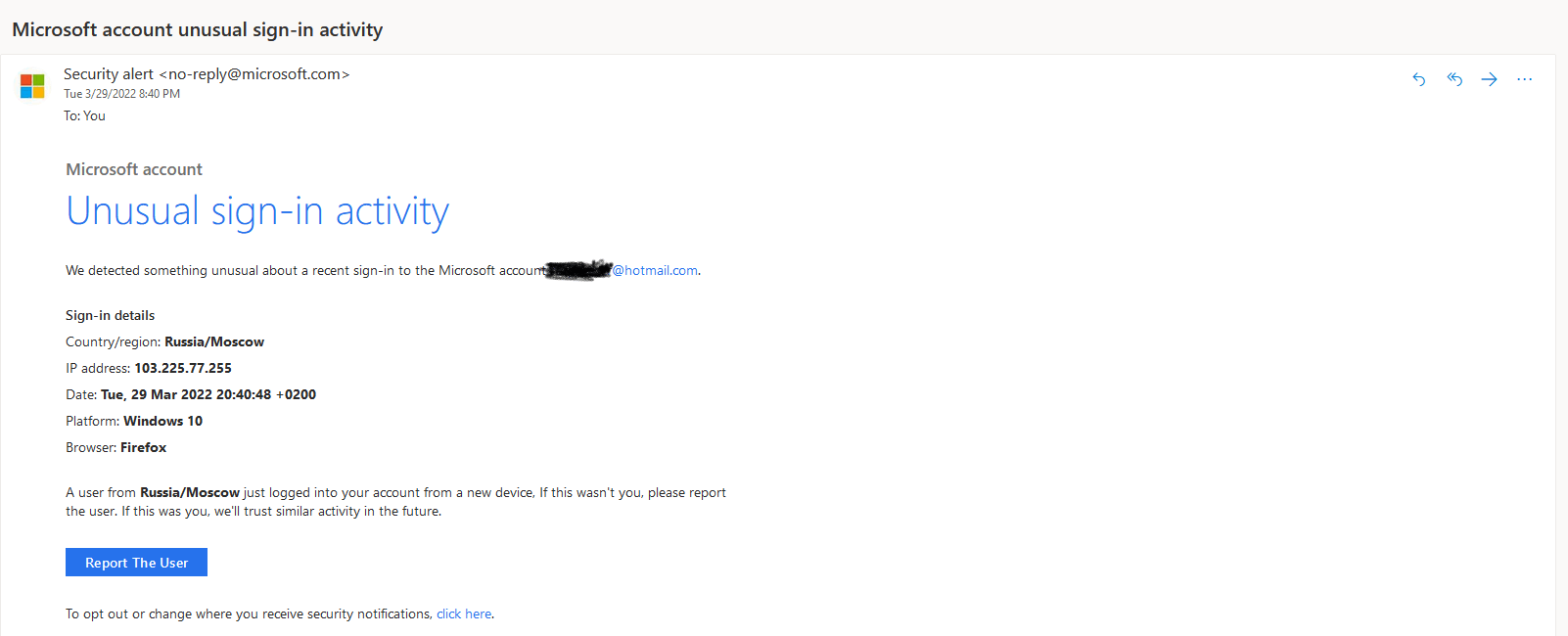
Dealing with an E-mail Spoof Attack in Office 365 based environment | Introduction | Part 1#12 - o365info
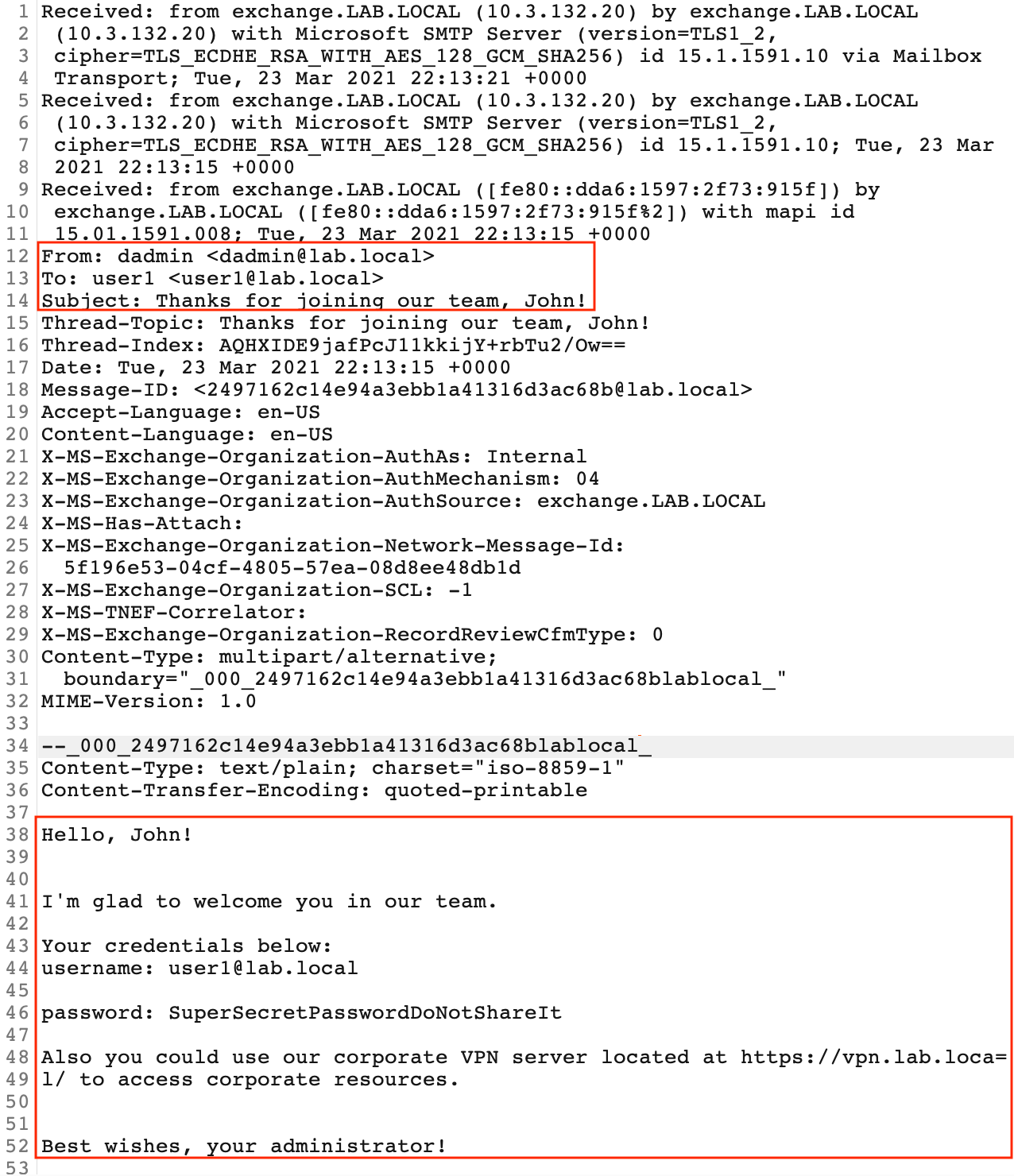
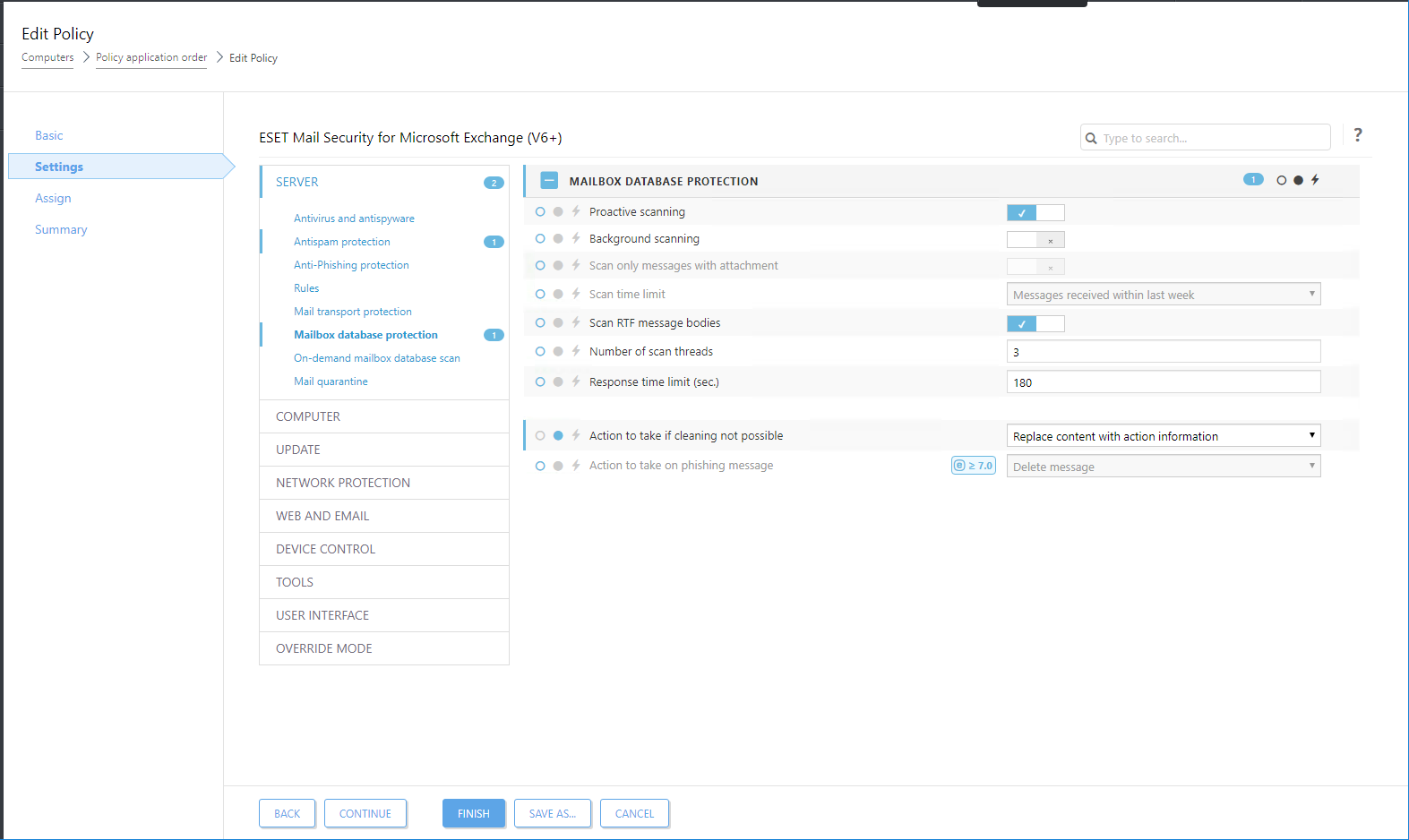
Hunting Down MS Exchange Attacks. Part 1. ProxyLogon (CVE-2021–26855, 26858, 27065, 26857) | by BI.ZONE | Medium
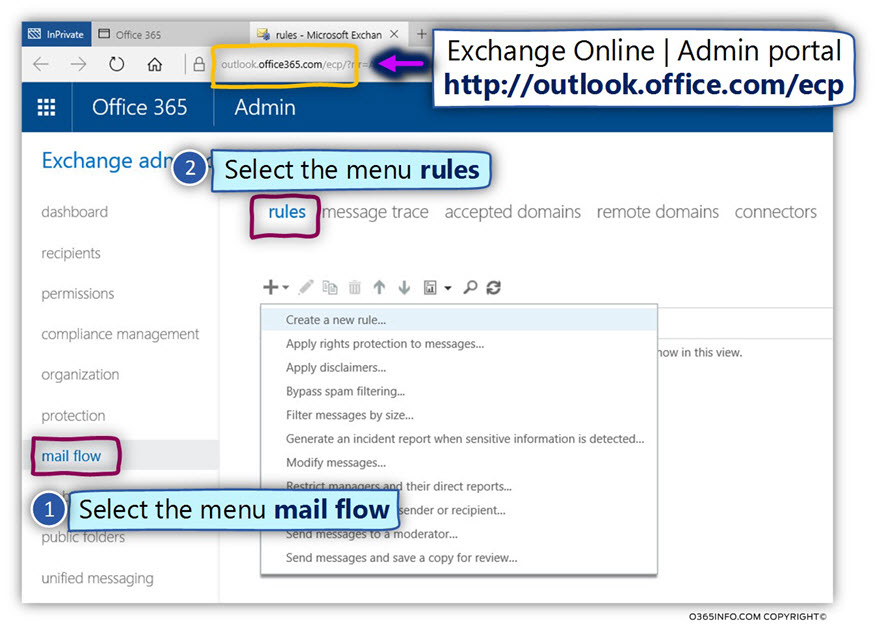
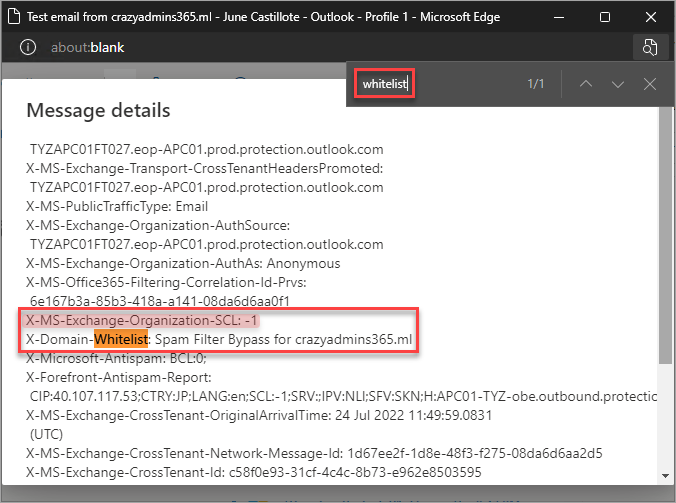
Detect spoof E-mail, mark spam , SCL | Detect spoof E-mail and mark the E-mail as spam using Exchange Online rule |Part 4#12 | o365info.com
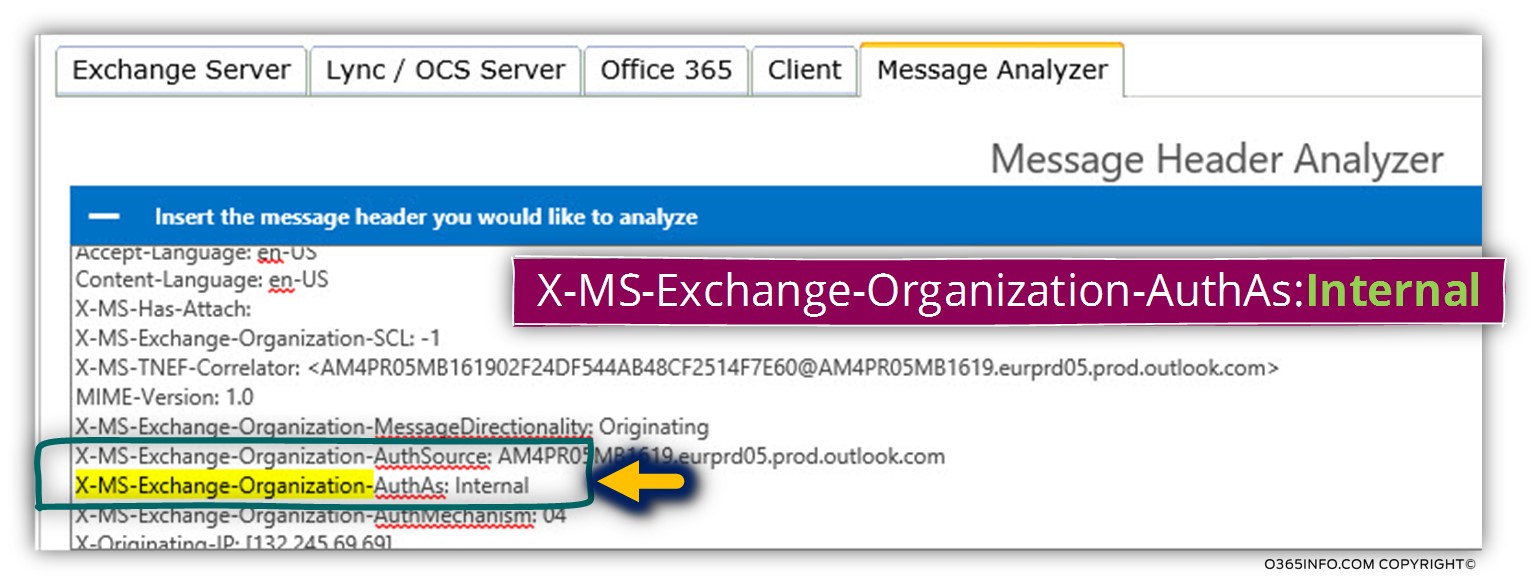
Dealing with an E-mail Spoof Attack in Office 365 based environment | Introduction | Part 1#12 - o365info
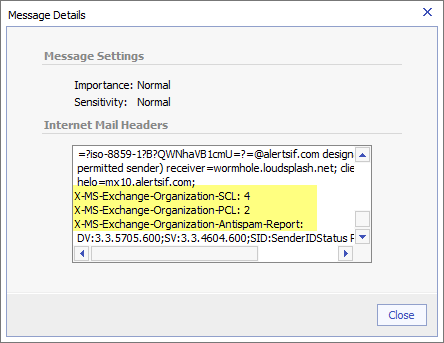
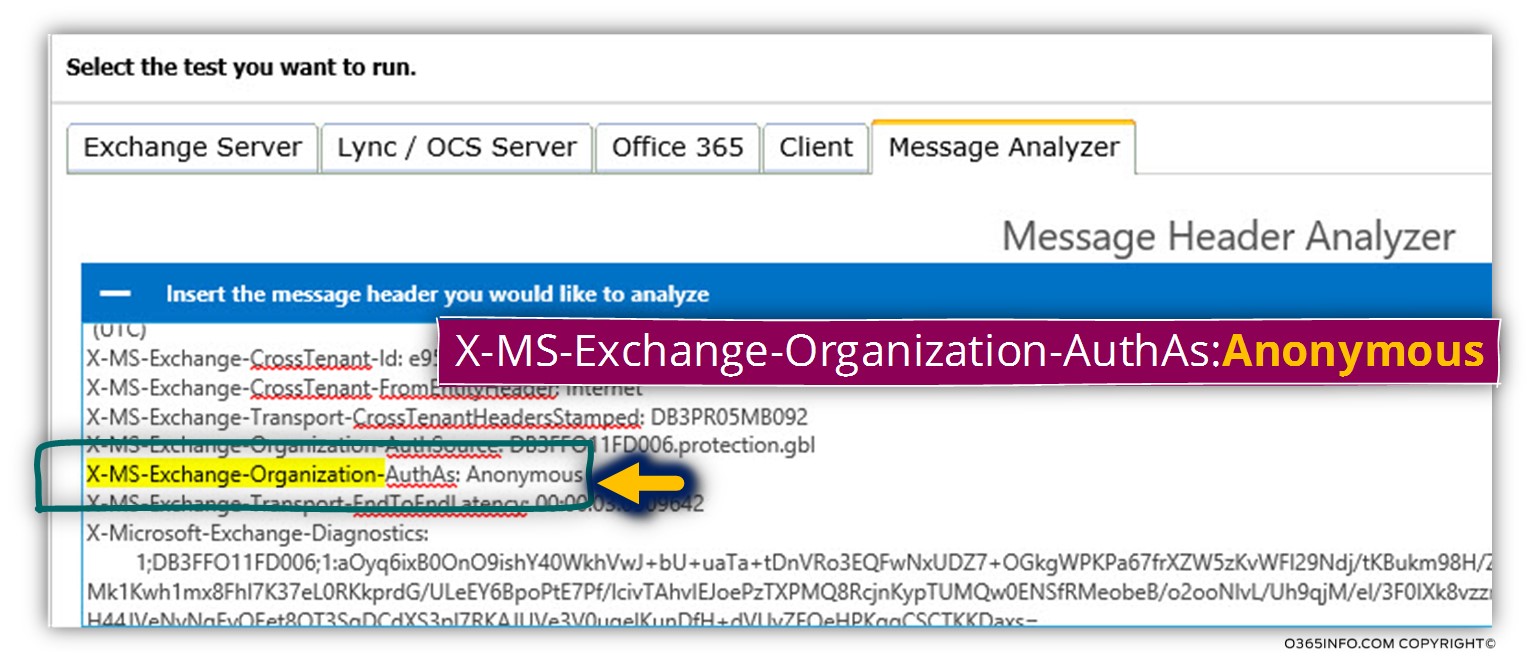
Exchangepedia | Header Firewall: Why spammers can't insert fake SCL (and other Exchange Organization) X headers